Services
/ our services /
Comprehensive Cybersecurity, Automation, and Digital Infrastructure Solutions
We bring comprehensive technological protection through a modular, scalable service design that integrates artificial intelligence and automation across every layer of the digital environment.
Defensive Security
Defend your digital perimeter with intelligent, continuous automated detection and rapid incident handling including SOCaaS, Threat Intelligence, vulnerability management, and more.
Offensive Security
Elevate your security posture with intelligent penetration testing, continuous attack simulation, and real-world adversary emulation.
GRC
Establish robust processes and ensure compliance with standards that align with regulatory requirements for IT and cloud-based security.
Development
Design scalable tech solutions: web and mobile development, along with modern technologies and cutting-edge practices.
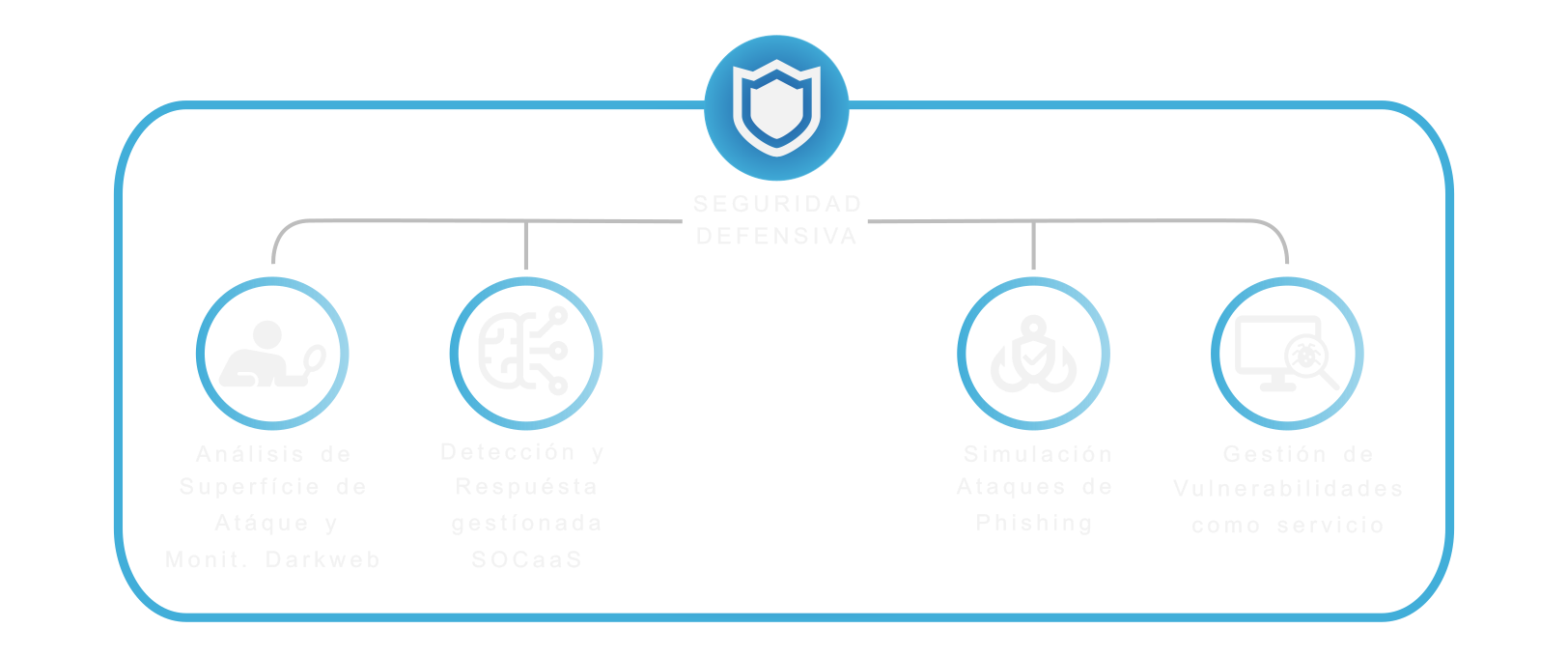
Attack Surface Assessment & Cyber Threat Intelligence
A managed cyber intelligence service that detects compromised credentials, data leaks, and malicious activity related to your organization — before it impacts your business.
Managed Detection and Response SOCaaS
A comprehensive service that combines SIEM, SOC, SOAR, ITSM, and threat intelligence with AI-driven analytics to detect, investigate, and respond to incidents quickly and efficiently.
Phishing Simulation
Identify awareness gaps and strengthen human response to phishing threats with safe, measurable, and fully customizable campaigns.
Vulnerability Management
Protect your infrastructure with a managed service that combines continuous monitoring, clear reporting, and expert guidance to keep you one step ahead of threats.
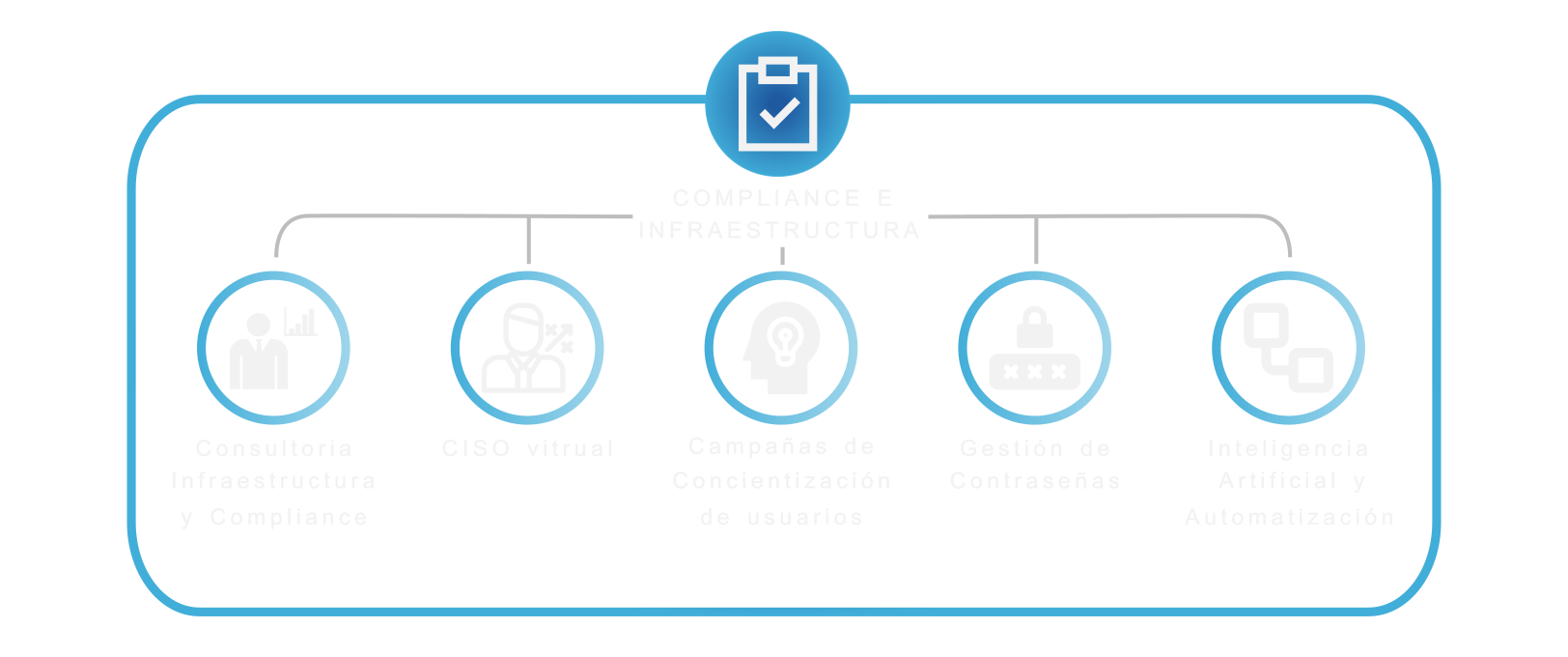
GRC Consultancy
We optimize your technology infrastructure and ensure that your organization complies with regulations and international standards, reducing risks and strengthening the trust of customers and partners.
Virtual CISO
An expert Chief Information Security Officer assigned as an external service, who leads the cybersecurity strategy, oversees risks, and ensures regulatory compliance.
Security Awareness
We design and implement awareness campaigns tailored to your organization's context, reducing the risk of human error and reinforcing a strong security culture.
Password Management
Secure storage solutions, multi-factor authentication, and best practices to reduce unauthorized access and improve digital hygiene.
Artificial Intelligence & Automation
We implement custom AI models and automated agents to transform internal processes, reduce costs, and increase operational efficiency.
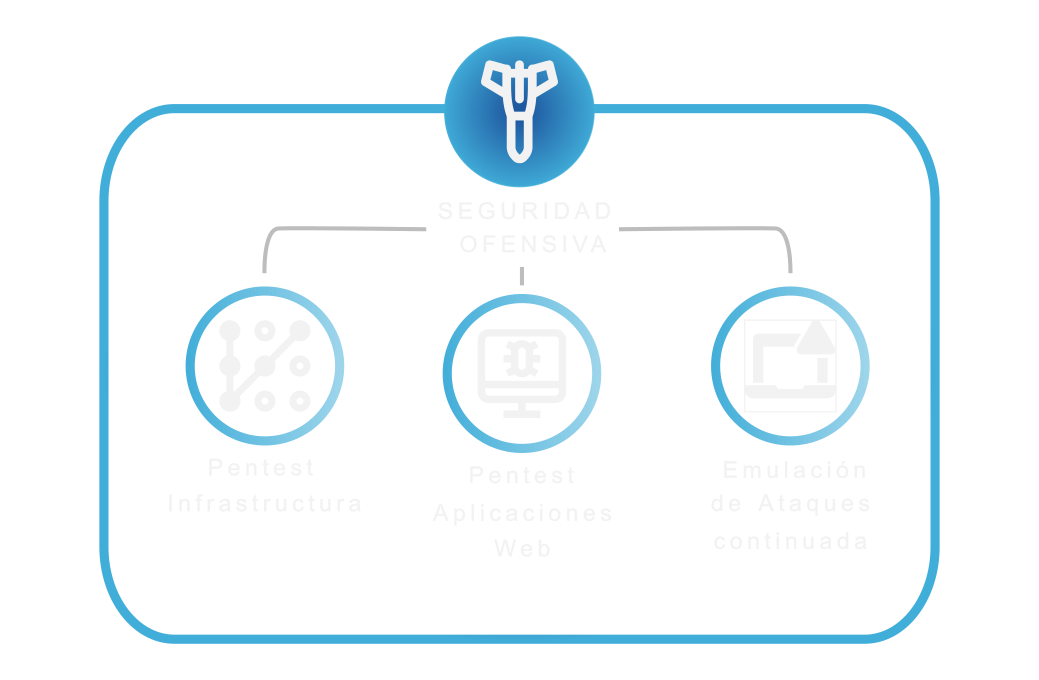
Infrastructure Pentest
Controlled simulation exercises that test your infrastructure against real attack techniques, always following best practices and maintaining constant communication with the client.
Web Application Pentesting
We identify vulnerabilities in your applications through controlled penetration testing, following standards such as OWASP and international reference frameworks.
Continued Attacks Emulation
We continuously simulate techniques used by real attackers to keep your security controls tuned and ready.
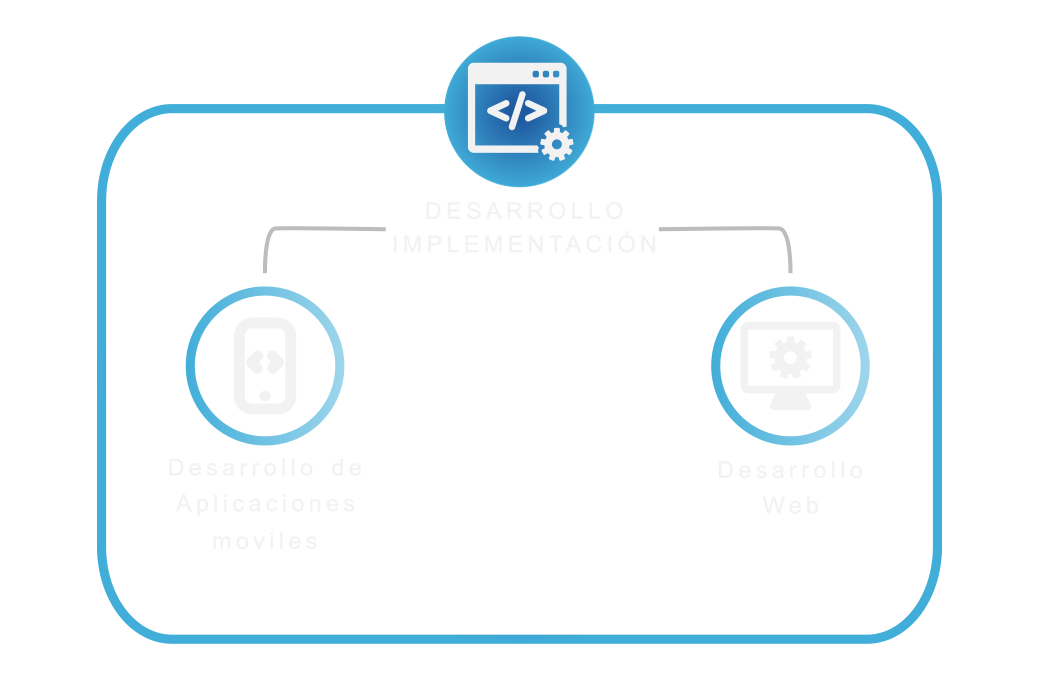
Mobile App Development
We design native and hybrid apps for iOS and Android, with a focus on user experience, integration, and scalability.
Web Development
We create portals, applications, and digital platforms tailored to your business, with a focus on performance, security, and user experience.
At Enclave Guard we're ready to help you
Get in touch with us and discover how we can optimize your IT infrastructure, protect your digital assets, and adapt to your pace of growth.
We work with companies, governments, and public institutions, delivering next-generation cybersecurity, automation, and IT infrastructure solutions tailored to real needs.
Contact Us
Start today and explore our solutions and services for your business.


