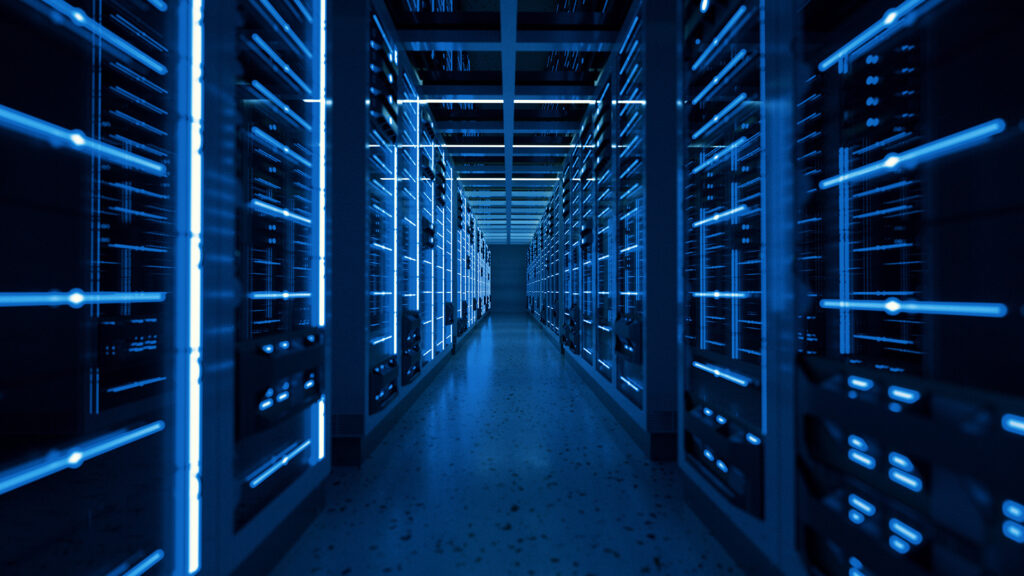
Infrastructure Pentest
Penetration testing on networks and critical systems
Controlled simulation exercises that test your infrastructure against real attack techniques, always following best practices and maintaining constant communication with the client.
The Infrastructure Pentest is an essential practice to understand the actual security level of corporate systems. Through advanced simulation techniques, intrusion attempts are replicated to compromise the network, servers, or even the entire domain of the organization.
These exercises can be carried out under Red Team approaches, with realistic scenarios and a predefined scope, ensuring that critical risks are identified and assessed before an attacker does. Our service follows industry best practices, such as OWASP, PTES (Penetration Testing Execution Standard), and OSSTMM, and is carried out with a constant communication channel with the client to ensure transparency and control throughout the entire process.
Infrastructure penetration testing requires a structured approach aligned with internationally recognized standards. The methodology is developed in four main phases: reconnaissance and enumeration — gathering information about the target systems, identifying exposed services and potential attack vectors; controlled intrusion and exploitation — executing techniques to validate real vulnerabilities, prioritizing the most critical ones; post-exploitation — including lateral movement, privilege escalation, and analysis to maximize information retrieval; and reporting and remediation — delivering a report with findings prioritized by impact and ease of exploitation, accompanied by a practical mitigation plan.
All findings are mapped to the MITRE ATT&CK framework, aligning the techniques used to contextualize within the global threat landscape and demonstrate traceability in every exercise. According to the Verizon DBIR 2023, over 80% of successful incidents originate from vulnerabilities exploited in misconfigured or unpatched infrastructure. With this service, the organization gains a clear view of its real risks, validated against attack techniques used by real-world malicious actors.

- Reconnaissance & Enumeration: Gathering information about target systems, identifying exposed services, potential attack vectors, and initial entry points.
- Controlled Intrusion & Exploitation: Executing real attack techniques to validate vulnerabilities, prioritizing the most critical ones based on impact and exploitability.
- Post-Exploitation Analysis: Lateral movement, privilege escalation, and in-depth analysis to assess the full extent of potential compromise within the infrastructure.
- MITRE ATT&CK Mapping: All findings mapped to the MITRE ATT&CK framework for full traceability and alignment with the global threat landscape.
/ benefits /
Core Service Benefits
Early Identification of Critical Risks
Discover and validate real vulnerabilities in your infrastructure before attackers do, enabling proactive remediation of the most impactful issues.
Alignment with Recognized Frameworks
Testing aligned with MITRE ATT&CK, PTES, OSSTMM, and OWASP ensures industry-standard quality, traceability, and actionable results.
Strengthened Organizational Resilience
Build a stronger security posture by understanding your real attack surface and implementing targeted remediation strategies.
/ how it works /
How Does the Service Work and What's Included?
At Enclave Guard we're ready to help you
Get in touch with us and discover how we can optimize your IT infrastructure, protect your digital assets, and adapt to your pace of growth.
We work with companies, governments, and public institutions, delivering next-generation cybersecurity, automation, and IT infrastructure solutions tailored to real needs.
Contact Us
Start today and explore our solutions and services for your business.


